The development pipeline for modern games no longer relies on a single building or closely supervised network. Now, game studios operate globally, with teams working simultaneously on shared codebases, digital assets, and even live gaming environments. This transformation has granted studios immense flexibility and capacity but has also raised an additional risk factor. Network security can no longer be an afterthought for IT departments; all studios, big or small, must consider it essential to their business functions.
For studios today, a single breach isn’t just a technical hiccup—it’s a potential multi-million dollar disaster. In fact, recent industry data shows that the gaming sector accounts for nearly 20% of all global DDoS attacks, and the frequency of targeted ransomware attacks on studios has risen by over 60% since 2023.
The Increasing Attack Surface in Game Development
The nature of game development makes the environment quite complex. A typical game development team is dependent on a mix of version control systems, cloud-based build sequence, digital asset management tools, and real-time collaboration platforms. All of these systems connect through networks that we must secure while keeping them accessible. The thing is, when studios expand and become fully distributed, the secure perimeter concept falls apart. Developers might be on the couch, in a co-working pod, or stuck in a train station. How do you trust data moving like that?
The security level of each network connection can be different and therefore it becomes very difficult to implement protection measures consistently. This change has played a part in the rise of the count of weaknesses in networks. Attackers now aren’t limited to just a single network when executing their attacks; they can use multiple devices, unsecured connections, and even misconfigured tools. Hence, a large number of studios are moving towards zero-trust security models, where by default, connections are not trusted and every access request has to be verified.
Key Threats Facing Development Teams

-
Intellectual Property Theft
Developing a game is mostly about creativity, and the look and feel of a game that the artists and designers come up with is very closely connected with the intellectual property a company has been building up over the years.
Concept art, 3D models, scripts, and proprietary engines are examples of assets that contain a lot of valuable intellectual property. People who commit cybercrimes or competitors could get hold of these assets if they do phishing, steal login credentials, or exploit the security vulnerabilities of the collaboration software they might discover.
Once the content is stolen, it can be uploaded on the internet, sold, and used to create similar projects without permission, adversely affecting both the profits and the image of the company.
-
Source Code Exposure
Your source code is the DNA of your project. If it leaks, you aren’t just losing secrets—you’re handing hackers a roadmap for creating cheats and exploits. This is especially dangerous for multiplayer or iGaming titles where fair play is tied directly to revenue. According to recent cybersecurity reports, the average cost of a data breach in the software industry has climbed to approximately $4.5 million per incident, a number that can easily bankrupt a mid-sized indie team.
-
Unsafe Remote Access
Remote access lets developers reach systems outside the office. But it’s a weak spot, hackers can slip in easily. They need to connect to test environments, cloud services, or internal tools from far away. At least in theory, security checks should catch these gaps. Common vulnerabilities include:
- Weak or reused passwords
- Lack of multi-factor authentication
- Misconfigured remote access tools
- Unsecured public Wi-Fi.
They get initial access, then climb permissions, move through the network, probably more or less without anyone noticing.
-
Geo-Restricted Testing Environments
Game makers want to see how their titles perform across regions. They use local servers, regional app stores, or tailored content to simulate real-world conditions.
In the absence of secure measures, developers might have to resort to unsafe methods to imitate these environments. This can lead to the exposure of sensitive data and the susceptibility of the data to being intercepted, especially during the period of pre-release when there is a necessity for confidentiality.
-
Data Breaches During Live Builds
Live service games need to launch new updates, patches, and content frequently. These updates are handled through automated pipelines that link the team of developers, staging and production environments. Therefore, in case a component of this pipeline gets compromised by cyber criminals, they can insert malicious code, cause disruption of services or even get access to sensitive information. The quick pace of today’s DevOps processes allows an undetected loophole to spread very fast across the system.
Why Security Is Moving Earlier in the Development Cycle
Security used to be considered a final obstacle before product release. However, this method is being abandoned nowadays. The price of fixing security holes at a late stage of development – or even after the product has been released – is far higher. Companies are gradually adjusting their security strategy by a “shift-left” method, which means they handle security first, to later work seamlessly with the second development phase.
These include:
- Incorporating secure coding principles from the beginning.
- Leveraging software packages that automatically check for security issues during production.
- Setting up authentication and authorization mechanisms in the software development process.
- Performing continuous network traffic analysis.
Doing security checks throughout the development cycle is one of the ways that teams can lower the level of risk while keeping up the pace of creating new things.
Building a Secure Development Environment
Game development teams are building layered security now to handle modern threats. They mix infrastructure shields with practices that matter to developers.
-
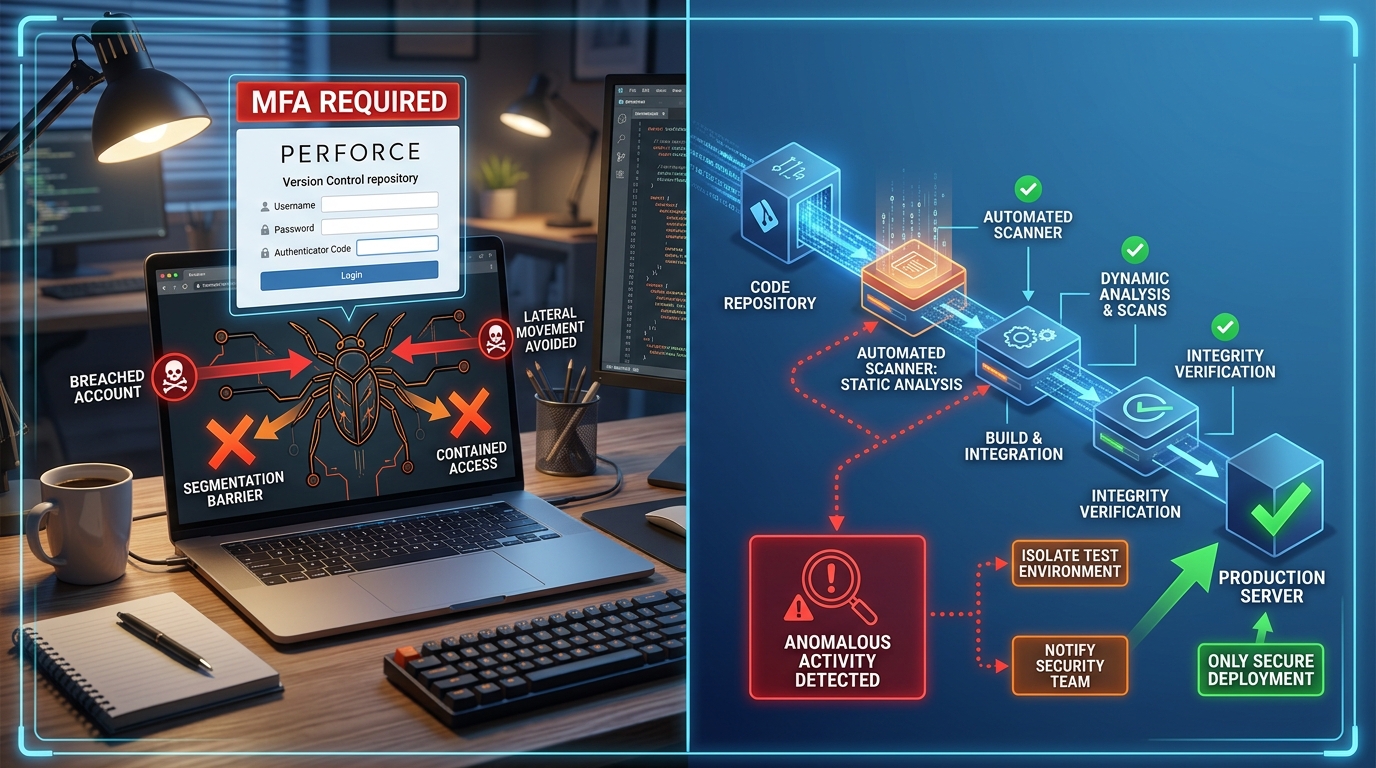
Secure Access Management
Role-based access control means each person, developer, designer or partners only sees what they need. That cuts down on damage if an account gets breached. Multi-factor authentication adds another layer. It makes unauthorized entry much less likely. Hard to ignore how this simple shift changes things.
-
Encrypted Communication Channels
Encryption is really the key to securing data transmission. No matter if it’s about sending codes, sharing files, or doing internal communication, the entire network traffic has to be encrypted.
One of the easiest ways for studios to encrypt their communication and secure the secret data of their projects when teams are distributed is to choose a good VPN provider. It’s even more necessary when working with international partners or accessing geographically restricted environments during tests.
-
Endpoint Security
Endpoints, e.g. developer laptops and mobile devices, tend to be the weakest link in network security. More and more studios require strict endpoint policies, such as the following:
- Device compliance requirements
- Endpoint detection and response (EDR) systems
- Regular software updates and patching
The aforementioned help in not only securing access to the networks from the outside but also in the detection of breaches to the networks that came through the endpoints.
-
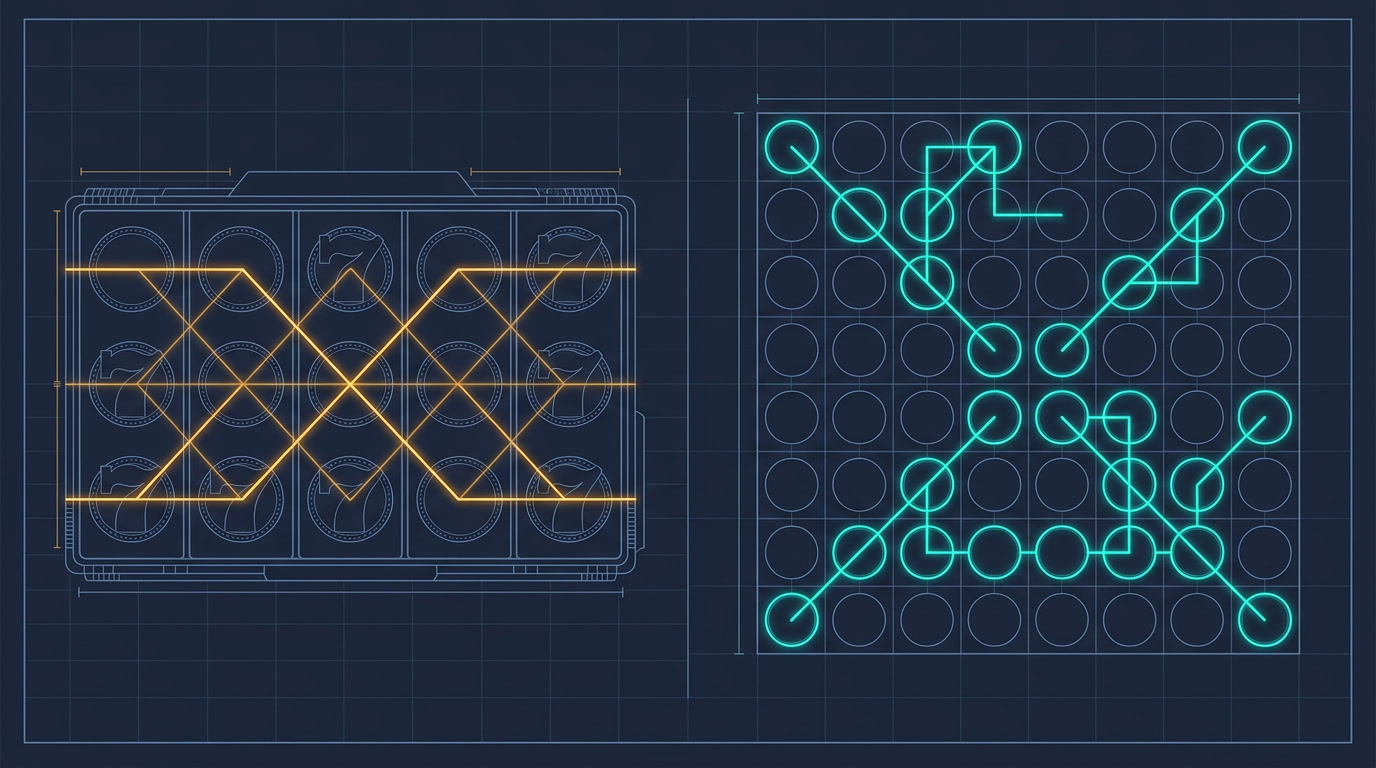
Secure CI/CD Pipelines
Continuous integration and deployment pipelines are necessary to modern game development. Access to build systems must be tightly restricted. Build integrity needs constant verification. Unusual activity during deployment should be detected immediately. A security incident may cause large-scale damage. These devices, being high-risk ones, should be handled accordingly.
-
Network Segmentation
Networks are split into zones like development, testing, and production. It stops breaches from spreading widely. If hackers get into one zone, they can’t just jump to others. This gives studios more control when teams work on big projects. So it probably helps keep sensitive data safer during busy times.
The Business Case for Stronger Network Security
Network security cannot be viewed as just a technical matter; rather, it should be regarded as a business-critical priority. Just one breach can have a serious financial impact, for instance, through downtime, loss of assets, or even disruption of development cycles. Another big problem is harm to reputation. Players expect developers to protect their data and deliver a safe game. A breach might break trust, which probably harms the company’s future growth.
There are also legal and regulatory factors. Since user data and internal materials need to be protected in accordance with data protection legislation and industry standards, non-compliance may result in fines and legal ramifications. Those developing game studios that take network security seriously not only prepare themselves well but also acquire a definite competitive edge. On top of that, they will be able to collaborate more effectively, increase their international presence, and implement their changes without any second thoughts as their systems will be secure.
Future Perspectives: Security as a Fundamental
As the gaming industry is constantly changing, network security is becoming a very crucial factor. Cloud gaming, cross-platform ecosystems, and AI-driven game development tools will make the development of gaming environments much more complex.
This change will lead to new possibilities but also to new threats. Those game studios that fail to adjust to the new situation will face increasingly sophisticated hacking attacks. Some very innovative teams are already considering security as a main discipline and are making it part of game development at the deepest level. They are security training their staff, security tools and methods are being implemented where every team member understands their role in protecting the network.
Conclusion
To sum up, network security is no longer an option but a necessity in the game development arena. In a sector where change is the only constant, keeping pace and working across borders have become defining features, protecting one’s digital assets and ensuring secure business operations stand out as major factors determining the success of a venture. Protecting a studio’s secrets and allowing a secure development pipeline are just part of the security issues that developers have to face. The list of difficulties that cross-functional teams encounter is not only tough but will keep on changing.
Nevertheless, by embracing a comprehensive security system that is always one step ahead of the bad guys and also making security part of every phase of the production process, game developers can go a long way in not only lessening the probability of an attack but also in minimizing the impact if an attack does happen. Making network security a top priority does not, in the end, mean that development will be hindered; rather, the opposite will be true. Once the teams have the assurance that collaboration can be done safely, that the sharing of these resources is without hesitation, and that security during updates is a given, these studios will be well-equipped to roll out top-notch gaming offerings in a market that is continuously growing in competitiveness.